2025-08-15 09:51
2025-08-15 09:51
2024-07-07 07:01
2024-02-07 19:23
2026-05-02 06:47
2026-04-12 07:56
2026-03-04 15:08
2019-11-27 17:19
2019-11-11 09:02
2019-07-21 13:03
Here is a roundup of today's hardware reviews. The AMD Ryzen 9 9950X3D2 Dual Edition redefines desktop performance by doubling down on 3D V-Cache across both chiplets without any asymmetric complexity. Lian Li and Gigabyte both showcased matching dark walnut wood designs that prove premium aesthetics can coexist with serious hardware engineering. AOC pushes past the usual OLED competition by delivering a blistering 360 Hz Fast-IPS display optimized specifically for competitive esports through G-SYNC Pulsar technology. You will also find reviews for a new Secretlab office chair, a Razer microphone featuring both USB and XLR connectivity, and a Navman dashcam that captures everything around your vehicle.
Casing: LIAN LI LANCOOL 217 Black Genuine Walnut Wood Case Review
CPUs: AMD Ryzen 9 9950X3D2 Dual Edition Review - Maximum Cache
Displays: AOC AGON PRO AG276QSG2 Gaming Monitor Review: When G-SYNC Pulsar OLED suddenly looks outdated in e-sports
Furniture: Secretlab Atlas review: The one you’ve been waiting for
Microphones: Razer Seiren V3 Pro Review: USB, XLR, and 32-bit float
Motherboards: GIGABYTE X870E AERO X3D DARK WOOD Motherboard Review
Other: Navman MiVue Smart True 4K Surround Dashcam Review - Seeing In All Directions At Once
[USN-8395-1] Netatalk vulnerabilities
[USN-8410-1] shell-quote vulnerability
[USN-8044-2] alsa-lib vulnerability
[USN-8398-2] nginx regression
[USN-8415-1] Vim vulnerabilities
[USN-8414-1] OpenSSL vulnerabilities
[USN-8414-2] OpenSSL vulnerabilities
[USN-8416-1] Go Networking vulnerability
[USN-8411-1] Lodash vulnerabilities
[USN-8156-2] GDK-PixBuf vulnerability
[USN-8412-1] QEMU vulnerabilities
[USN-8413-1] Cyborg vulnerabilities
SUSE-SU-2026:2306-1: important: Security update for perl-Protocol-HTTP2
SUSE-SU-2026:2307-1: important: Security update for nginx
SUSE-SU-2026:2310-1: important: Security update for the Linux Kernel
SUSE-SU-2026:2311-1: moderate: Security update for avahi
openSUSE-SU-2026:20921-1: important: Security update for elemental-toolkit
openSUSE-SU-2026:20926-1: moderate: Security update for python-requests
openSUSE-SU-2026:20925-1: moderate: Security update for polkit
openSUSE-SU-2026:20919-1: moderate: Security update for agama-web-ui
openSUSE-SU-2026:20924-1: important: Security update for elemental-system-agent
openSUSE-SU-2026:20920-1: important: Security update for elemental-register
openSUSE-SU-2026:10965-1: moderate: ack-3.10.0-1.1 on GA media
openSUSE-SU-2026:10968-1: moderate: perl-CryptX-0.89.0-2.1 on GA media
openSUSE-SU-2026:10966-1: moderate: amazon-ssm-agent-3.3.4624.0-2.1 on GA media
openSUSE-SU-2026:10961-1: moderate: ggml-devel-9500-1.1 on GA media
SUSE-SU-2026:2325-1: important: Security update for kubernetes1.26
RLSA-2026:22644: Important: samba security update
RHSA-2026:24716: Important: yggdrasil security update
RHSA-2026:24719: Important: thunderbird security update
RHSA-2026:24718: Important: thunderbird security update
RHSA-2026:24758: Important: libyang security update
RHSA-2026:24722: Moderate: libsoup security update
RHSA-2026:24721: Important: thunderbird security update
RHSA-2026:24717: Important: thunderbird security update
RHSA-2026:24851: Important: bind security update
RHSA-2026:24846: Important: thunderbird security update
RHSA-2026:24814: Important: kpatch-patch security update
RHSA-2026:24761: Important: Red Hat Ansible Automation Platform 2.5 Product Security and Bug Fix Update
RHSA-2026:24762: Important: Red Hat Ansible Automation Platform 2.6 Product Security and Bug Fix Update
RHSA-2026:24755: Important: firefox security update
RHSA-2026:24844: Important: thunderbird security update
Fedora 43 Update: xorg-x11-server-21.1.23-1.fc43
Fedora 43 Update: firefox-151.0.3-1.fc43
Fedora 43 Update: exim-4.99.4-1.fc43
Fedora 43 Update: putty-0.84-1.fc43
Fedora 43 Update: pcs-0.12.2-2.fc43
Fedora 44 Update: exim-4.99.4-1.fc44
Fedora 44 Update: putty-0.84-1.fc44
Fedora 44 Update: pcs-0.12.2-2.fc44
[DLA 4624-1] openssl security update
[DSA 6335-1] openssl security update
[DSA 6334-1] poppler security update
[DSA 6333-1] mistral security update
[DSA 6332-1] okular security update
ALSA-2026:24339: bind security update (Important)
ALSA-2026:24545: libyang security update (Important)
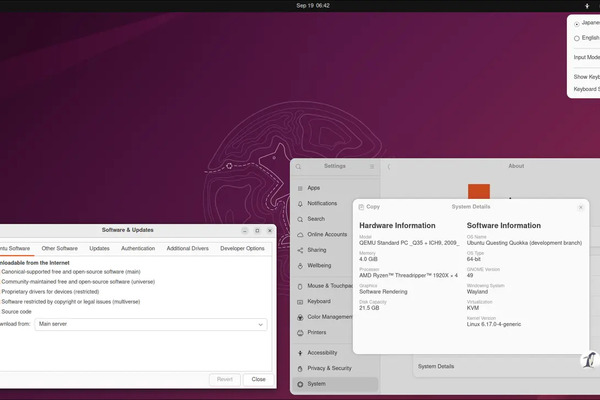
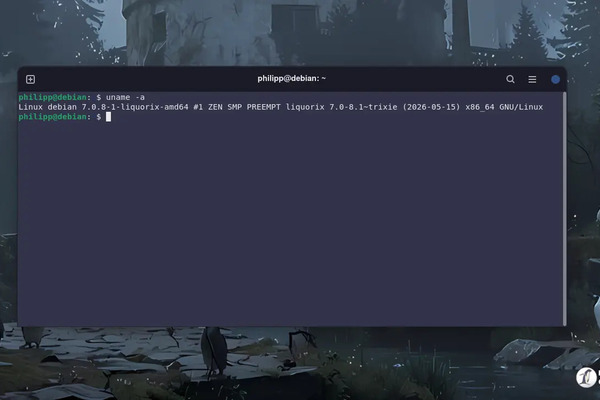
The XanMod Kernel 6.18.35 LTS and 7.0.12 drop into Debian-based systems with a heavy focus on fixing memory leaks in USB and Bluetooth drivers while tightening networking stack bounds checking. Official repositories make the five-minute installation straightforward, though users must register the GPG key and add the correct distribution codename before running the package manager. Systems relying on external kernel modules need the dkms and build dependency packages installed first to prevent driver compilation failures after the reboot. Verifying hardware detection and proprietary graphics modules on the first boot prevents silent failures, and the automated repository updates keep the optimized scheduler and memory tweaks current without manual intervention.
The latest hardware roundup highlights the be quiet! Dark Rock 6 and Pro 6 CPU coolers, which rely on dense fin arrays and intelligent switching to rival liquid cooling solutions. Keyboard enthusiasts will appreciate the IQUNIX Magi96 Pro for its robust aluminum chassis and satisfying typing acoustics in a compact low profile design. Performance seekers can look toward Patriot Viper Elite 5 Ultra DDR5 RAM, which delivers blistering 8000 MT/s speeds while keeping voltage requirements modest. The collection wraps up with mixed results for mobile connectivity and data management, pointing out the Travlfi JourneyGo hotspot as budget friendly but feature heavy, while praising the Intel powered QNAP TS-855eU NAS for its versatile storage and virtualization capabilities.
Cooling: be quiet! Dark Rock 6 & Dark Rock Pro 6 CPU Coolers Review
Input: IQUNIX Magi96 Pro Aluminum Low Profile Mechanical Keyboard Review - Premium Build, Satisfying Sound
Memory: Patriot Viper Elite 5 Ultra RGB DDR5-8000 48 GB CL36 Review
Networking: Travlfi JourneyGo 5G mobile hotspot review – Affordably priced, but lacking in performance and features
Storage: QNAP TS-855eU NAS in review - Intel C5125, 8+2 bays and virtualization, is this still a network storage device?
The openSUSE Leap 16.1 Beta arrives with its proven hybrid model, blending enterprise-grade core packages with community desktop improvements for a system that refuses to break during routine updates. Users who have wrestled with rolling releases will appreciate the extended support window, which gives administrators and home users plenty of time to verify hardware compatibility before committing to the final release. The beta ships with a refreshed package manager that catches dependency conflicts early, preventing the kind of silent system breaks that usually force a full reinstall. Anyone looking for a reliable daily driver or a stable server base should test this release, though gamers and cutting edge developers might want to stick to dedicated testing branches until the official launch.
Bazzite Linux 44.20260608 prioritizes handheld stability and NVIDIA driver compatibility by pinning a patched kwin build to prevent Wayland session crashes. The release also adjusts Sunshine for better gamepad capture on KDE desktops and aligns session shortcuts closer to SteamOS behavior. Rather than introducing flashy new features, the update delivers routine package bumps for core components like libinput, Steam, and selinux-policy to quietly fix known friction points. Current users can switch to this version quickly using the bazzite-rollback-helper, which handles the ostree transaction and preserves existing Flatpak containers without requiring a fresh install.
[USN-8399-1] Pillow vulnerabilities
[USN-8400-1] poppler vulnerability
[USN-8398-1] nginx vulnerability
[USN-8397-1] libjxl vulnerability
[USN-8405-1] CUPS vulnerabilities
[USN-8387-1] Inetutils vulnerabilities
[USN-8404-1] Transmission vulnerability
[USN-8402-1] systemd vulnerabilities
[USN-8403-1] Kea DHCP vulnerability
[USN-8408-1] Twig vulnerability
[USN-8407-1] strongSwan vulnerability
[USN-8406-1] Net::CIDR::Lite vulnerabilities
[USN-8401-1] Netty vulnerabilities
[USN-8349-2] rsync regression
openSUSE-SU-2026:0193-1: important: Security update for epiphany
openSUSE-SU-2026:20914-1: important: Security update for ffmpeg-4
openSUSE-SU-2026:20916-1: critical: Security update for chromium
openSUSE-SU-2026:20911-1: moderate: Security update for NetworkManager
openSUSE-SU-2026:20908-1: important: Security update for perl-XML-LibXML
openSUSE-SU-2026:20910-1: moderate: Security update for uriparser
openSUSE-SU-2026:20909-1: moderate: Security update for dpkg
openSUSE-SU-2026:20912-1: important: Security update for the Linux Kernel
SUSE-SU-2026:2298-1: moderate: Security update for python311
SUSE-SU-2026:2297-1: moderate: Security update for avahi
openSUSE-SU-2026:0194-1: important: Security update for chromium
openSUSE-SU-2026:10956-1: moderate: libopenvswitch-3_7-0-3.7.1-34.1 on GA media
openSUSE-SU-2026:10953-1: moderate: gleam-1.17.0-1.1 on GA media
openSUSE-SU-2026:10957-1: moderate: perl-HTML-Parser-3.850.0-1.1 on GA media
openSUSE-SU-2026:10958-1: moderate: chromedriver-149.0.7827.53-2.1 on GA media
openSUSE-SU-2026:10955-1: moderate: libmozjs-140-0-140.10.1-2.1 on GA media
openSUSE-SU-2026:10954-1: moderate: kernel-devel-7.0.11-1.1 on GA media
openSUSE-SU-2026:10951-1: moderate: perl-Net-CIDR-Set-0.210.0-1.1 on GA media
openSUSE-SU-2026:0195-1: important: Security update for keybase-client
SUSE-SU-2026:2302-1: moderate: Security update for firewalld
SUSE-SU-2026:2301-1: moderate: Security update for mutt
RHSA-2026:24381: Important: kernel security update
RHSA-2026:24470: Important: podman security update
RHSA-2026:24383: Moderate: libarchive security update
RHSA-2026:24368: Important: bind9.18 security update
RHSA-2026:24365: Important: unbound security update
RHSA-2026:24343: Important: kernel security update
RHSA-2026:24339: Important: bind security update
RHSA-2026:24336: Important: .NET 9.0 security update
RHSA-2026:24508: Important: firefox security update
RHSA-2026:24510: Important: firefox security update
RHSA-2026:24509: Important: firefox security update
RHSA-2026:24500: Important: bind security update
RHSA-2026:24386: Important: podman security update
RHSA-2026:24371: Important: frr security update
RHSA-2026:24370: Important: frr10 security update
RHSA-2026:24369: Important: unbound security update
RHSA-2026:24367: Important: bind security update
RHSA-2026:24683: Important: krb5 security update
RHSA-2026:24686: Important: krb5 security update
RHSA-2026:24685: Important: krb5 security update
RHSA-2026:24545: Important: libyang security update
RHSA-2026:24516: Important: firefox security update
RHSA-2026:24511: Important: firefox security update
ELSA-2026-22112 Important: Oracle Linux 8 go-toolset:ol8 security update
ELSA-2026-22644 Important: Oracle Linux 8 samba security update
ELSA-2026-23360 Important: Oracle Linux 8 bind9.16 security update
ELSA-2026-23258 Important: Oracle Linux 8 kernel security update
ELSA-2026-22730 Moderate: Oracle Linux 8 vim security update
ELSA-2026-24339 Important: Oracle Linux 8 bind security update
ELBA-2026-50303 Oracle Linux 9 grub2 bug fix update
ELSA-2026-17618 Moderate: Oracle Linux 7 ImageMagick security update
Fedora 43 Update: objfw-1.5.5-1.fc43
Fedora 43 Update: mingw-objfw-1.5.5-1.fc43
Fedora 44 Update: mingw-objfw-1.5.5-1.fc44
Fedora 44 Update: objfw-1.5.5-1.fc44
Fedora 44 Update: tailscale-1.98.4-1.fc44
Fedora 44 Update: sentencepiece-0.2.1-1.fc44
[DSA 6329-1] tomcat11 security update
[DSA 6328-1] tomcat10 security update
[DLA 4623-1] jackson-core security update
[DLA 4622-1] libxml2 security update
[DSA 6331-1] keystone security update
ALSA-2026:24365: unbound security update (Important)
ALSA-2026:18134: kernel security update (Moderate)
ALSA-2026:23329: kernel security update (Important)
ALSA-2026:21557: kernel security update (Important)
ALSA-2026:24338: bind security update (Important)
ALSA-2026:19569: kernel security update (Important)
ALSA-2026:24340: frr security update (Important)
[ Archive ]