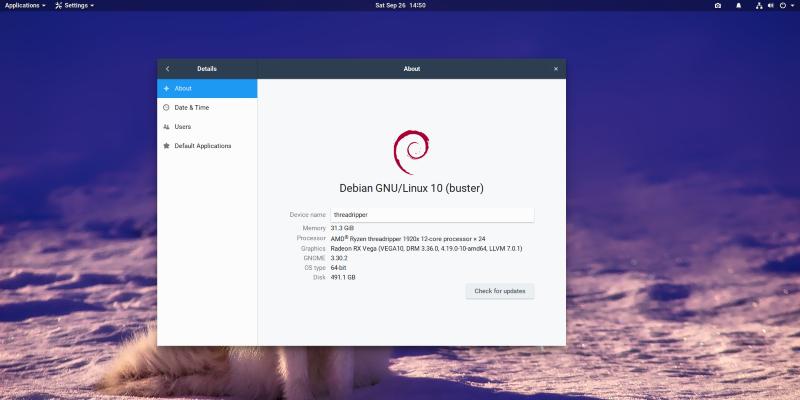
Updated Debian 10: 10.8 released
The Debian project is pleased to announce the eighth update of its stable distribution Debian 10 (codename buster). This point release mainly adds corrections for security issues, along with a few adjustments for serious problems. Security advisories have already been published separately and are referenced where available.
Please note that the point release does not constitute a new version of Debian 10 but only updates some of the packages included. There is no need to throw away old buster media. After installation, packages can be upgraded to the current versions using an up-to-date Debian mirror.
Those who frequently install updates from security.debian.org won't have to update many packages, and most such updates are included in the point release.
New installation images will be available soon at the regular locations.
Upgrading an existing installation to this revision can be achieved by pointing the package management system at one of Debian's many HTTP mirrors. A comprehensive list of mirrors is available at:
Miscellaneous Bugfixes
This stable update adds a few important corrections to the following packages:
Package Reason atftp Fix denial of service issue [CVE-2020-6097] base-files Update /etc/debian_version for the 10.8 point release ca-certificates Update Mozilla CA bundle to 2.40, blacklist expired AddTrust External Root cacti Fix SQL injection issue [CVE-2020-35701] and stored XSS issue cairo Fix mask usage in image-compositor [CVE-2020-35492] choose-mirror Update mirror list cjson Fix infinite loop in cJSON_Minify clevis Fix initramfs creation; clevis-dracut: Trigger initramfs creation upon installation cyrus-imapd Fix version comparison in cron script debian-edu-config Move host keytabs cleanup code out of gosa-modify-host into a standalone script, reducing LDAP calls to a single query debian-installer Use 4.19.0-14 Linux kernel ABI; rebuild against proposed-updates debian-installer-netboot-images Rebuild against proposed-updates debian-installer-utils Support partitions on USB UAS devices device-tree-compiler Fix segfault on dtc -I fs /proc/device-tree didjvu Add missing build-dependency on tzdata dovecot Fix crash when searching mailboxes containing malformed MIME messages dpdk New upstream stable release edk2 CryptoPkg/BaseCryptLib: fix NULL dereference [CVE-2019-14584] emacs Don't crash with OpenPGP User IDs with no e-mail address fcitx Fix input method support in Flatpaks file Increase name recursion depth to 50 by default geoclue-2.0 Check the maximum allowed accuracy level even for system applications; make the Mozilla API key configurable and use a Debian-specific key by default; fix display of the usage indicator gnutls28 Fix test suite error caused by expired certificate grub2 When upgrading grub-pc noninteractively, bail out if grub-install fails; explicitly check whether the target device exists before running grub-install; grub-install: Add backup and restore; don't call grub-install on fresh install of grub-pc highlight.js Fix prototype pollution [CVE-2020-26237] intel-microcode Update various microcode iproute2 Fix bugs in JSON output; fix race condition that DOSes the system when using ip netns add at boot irssi-plugin-xmpp Do not trigger the irssi core connect timeout prematurely, thus fixing STARTTLS connections libdatetime-timezone-perl Update for new tzdata version libdbd-csv-perl Fix test failure with libdbi-perl 1.642-1+deb10u2 libdbi-perl Security fix [CVE-2014-10402] libmaxminddb Fix heap-based buffer over-read [CVE-2020-28241] lttng-modules Fix build on kernel versions >= 4.19.0-10 m2crypto Fix compatibility with OpenSSL 1.1.1i and newer mini-buildd builder.py: sbuild call: set '--no-arch-all' explicitly net-snmp snmpd: Add cacheTime and execType flags to EXTEND-MIB node-ini Do not allow invalid hazardous string as section name [CVE-2020-7788] node-y18n Fix prototype pollution issue [CVE-2020-7774] nvidia-graphics-drivers New upstream release; fix possible denial of service and information disclosure [CVE-2021-1056] nvidia-graphics-drivers-legacy-390xx New upstream release; fix possible denial of service and information disclosure [CVE-2021-1056] pdns Security fixes [CVE-2019-10203 CVE-2020-17482] pepperflashplugin-nonfree Turn into a dummy package taking care of removing the previously installed plugin (no longer functional nor supported) pngcheck Fix buffer overflow [CVE-2020-27818] postgresql-11 New upstream stable release; security fixes [CVE-2020-25694 CVE-2020-25695 CVE-2020-25696] postsrsd Ensure timestamp tags aren't too long before trying to decode them [CVE-2020-35573] python-bottle Stop allowing ; as a query-string separator [CVE-2020-28473] python-certbot Automatically use ACMEv2 API for renewals, to avoid issues with ACMEv1 API removal qxmpp Fix potential SEGFAULT on connection error silx python(3)-silx: Add dependency on python(3)-scipy slirp Fix buffer overflows [CVE-2020-7039 CVE-2020-8608] steam New upstream release systemd journal: do not trigger assertion when journal_file_close() is passed NULL tang Avoid race condition between keygen and update tzdata New upstream release; update included timezone data unzip Apply further fixes for CVE-2019-13232 wireshark Fix various crashes, infinite loops and memory leaks [CVE-2019-16319 CVE-2019-19553 CVE-2020-11647 CVE-2020-13164 CVE-2020-15466 CVE-2020-25862 CVE-2020-25863 CVE-2020-26418 CVE-2020-26421 CVE-2020-26575 CVE-2020-28030 CVE-2020-7045 CVE-2020-9428 CVE-2020-9430 CVE-2020-9431] Security Updates
This revision adds the following security updates to the stable release. The Security Team has already released an advisory for each of these updates:
Removed packages
The following packages were removed due to circumstances beyond our control:
Package Reason compactheader Incompatible with current Thunderbird versions Debian Installer
The installer has been updated to include the fixes incorporated into stable by the point release.
URLs
The complete lists of packages that have changed with this revision:
The current stable distribution:
Proposed updates to the stable distribution:
stable distribution information (release notes, errata etc.):
Security announcements and information:
About Debian
The Debian Project is an association of Free Software developers who volunteer their time and effort in order to produce the completely free operating system Debian.
The eighth update of Debian GNU/Linux 10 is now available. This point release mainly adds corrections for security issues, along with a few adjustments for serious problems.